In the war between malicious actors and regular users, there’s a constant evolution of attacks and a corresponding adaptation of defenses.
A recently-discovered, attack takes advantage of one of the most annoying online verification measures – CAPTCHA – to download malicious software onto your computer.
(Fun fact, CAPTCHA is an acronym for “Completely Automated Public Turing test to tell Computers and Humans Apart”.)
What is Captcha?
CAPTCHA is how many online services tell if form submissions (like creating an account or posting a comment) are being done by a computer or a human.
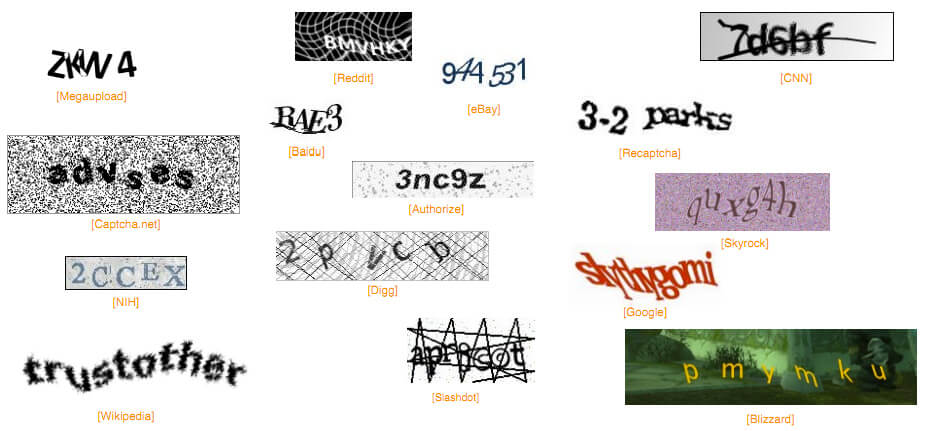
There are many different kinds of CAPTCHA. Some of the most common include typing distorted letters into a box, or Google’s newest CAPTCHA used to train its Waymo cars.
One thing that they all share, though, is that we have been trained to execute the CAPTCHA actions without much of a second thought.
And that’s why this latest malware campaign is so effective.
How the Fake Captcha Attack Works
A BleepingComputer post has complete information, but here’s the TL;DR version:

- A random link is sent to a user, and onn that page is an embedded YouTube video.
- Clicking on the “Play” button downloads a file. The file is often called “console.exe”.
- Since the page downloaded a .exe file, Chrome shows the “This type of file can harm your computer” warning dialogue box.
- Here’s where it gets clever. After clicking on the “Play” button (which downloaded a file), the website displays a fake CAPTCHA.
- In BleepingComputer’s example, the CAPTCHA instructs the user to press the following keys: B, S, Tab, A, F, and Enter.
- While the letter keys don’t do anything, pressing the Tab key selects the “Keep” option in the Chrome warning dialogue box, and pressing Enter will act as a click, keeping the infected file.
- Downloading the file by itself won’t do anything, but if you run the malicious console.exe file, then the malware will be installed on your computer.
This malware will steal account credentials for as many online accounts as it can, download additional malware to your computer, and it can also execute remote commands sent by the malware controllers.
More information (including pictures of what to look out for) can be found on BleepingComputer.

Leave a Reply
You must be logged in to post a comment.